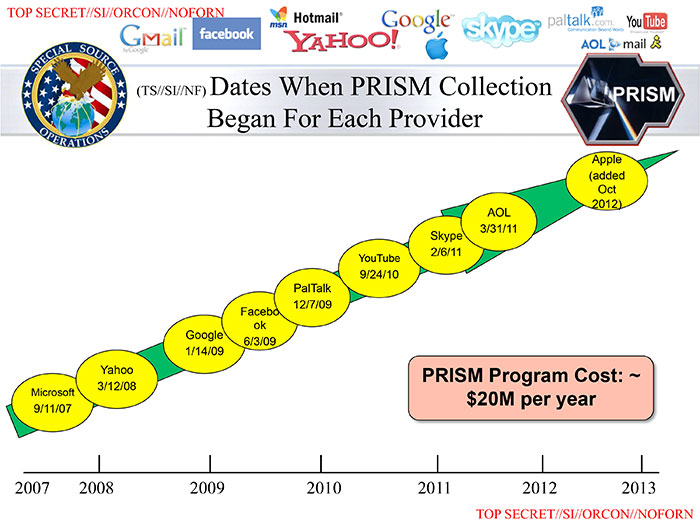
Prism, a clandestine system of spying on people involving many large internet companies was revealed by the newspapers the Washington Post and the Guardian on 6 June 2013 having – it is later revealed – been leaked by Edward Snowden.
The leaked documents revealed a routine, automated system of spying on people involving many of the largest internet companies – Microsoft, Yahoo, Google, Facebook, YouTube, Apple, etc. The leaked documents were in the form of a Powerpoint presentation presumably used to train intelligence agents. The Guardian further claimed on 7 June 2013 that the UK’s covert surveillance centre GCHQ had access to the NSA’s Prism system from at least 2010.
Prism raises some big issues: First, that people – including US citizens – are spied on as a matter of routine. Second, that huge internet companies have so readily assisted spying on people and then strangely denied it so strongly despite there being overwhelming evidence. Third, the closeness of huge corporations and the US state.
US and UK law is similar in that covert spying should be authorised rather than routine. The normal and expected procedure is that there exists an element of suspicion of some serious crime and some legal authority e.g. a warrant would be issued. Prism seems far more routine and relaxed. Safeguards to prevent US authorities spying on US citizens appear to be so weak as to be effectively useless.
Wikipedia suggests that gagging orders have been served on the big internet companies so they are legally prevented from disclosing their involvement in Prism. We have similar gagging orders in the UK under the Regulation of Investigatory Powers Act.
I was thinking more about interpreting the literal meanings of the carefully-crafted denials.
Microsoft: “We provide customer data only when we receive a legally binding order or subpoena to do so, and never on a voluntary basis. In addition we only ever comply with orders for requests about specific accounts or identifiers. If the government has a broader voluntary national security program to gather customer data we don’t participate in it.”
So they’ve had a legally binding order or subpoena to disclose information, only respond to specific accounts or identifiers (what about all or every? is that specific enough?) and don’t do it voluntary. Not nuch of a denial really.
Yahoo!: “Yahoo! takes users’ privacy very seriously. We do not provide the government with direct access to our servers, systems, or network.”
… but we do provide them with indirect access?
Google: “Google cares deeply about the security of our users’ data. We disclose user data to government in accordance with the law, and we review all such requests carefully. From time to time, people allege that we have created a government ‘back door‘ into our systems, but Google does not have a backdoor for the government to access private user data.”
According to law, no backdoor. What about the front door keys? ‘backdoor’ has a specific meaning which is about unauthorised access.
The internet is a network of servers. What if the NSA owned the servers that surround these internet companies? No need for a back door then. There’s no need to access a system if you can access all traffic that goes in and out. If I had a router on the internet I could inspect, store and analyse all traffic flowing through it: I just need to put it next – in the route – to an interesting machine.
I would be concerned by the closeness of government and corporatism [corporations] if I were some foreign governments. Where’s the payback? Are these corporations not going to use this spying technology for corporate advantage? There’s also the issue about Mussolini’s definition of Fascism. These corporations are playing along with the BS. Is there also a payback that they’re able to enrich themselves by evading taxes?
We live in an era of fake manufactured terrorism being the quite ridiculous dominant ideology. People are controlled through fear. Corrupt governments need to spy on their people to maintain control. There are very dangerous people that actually have a mind of their own. Governments and their political apointees will use this technology to corruptly maintain control. There are plenty of examples of USUK governments engaging in mass deception recently.
14/06/13 UPDATE
An interesting article here discusses US government spies ‘tapping’ AT&T in 2006:
In 2002, a visitor to his AT&T office in San Francisco identified himself as an NSA representative. The official interviewed Klein’s colleague, who said he was given top-secret government clearance soon after the encounter.
A year later when Klein he saw the colleague installing a special room, which only that person was allowed to enter.
When the colleague retired in 2004, he gave Mr Klein several documents, including highly technical wiring diagrams. The diagrams showed AT&T’s electronic communications flowed through a “splitter” which created identical copies of the digital material.
One copy continued on to its intended destination of consumer email in-boxes, phones and the like. The other copy flowed into the secret room.
It was clear that the NSA was looking at everything and not just foreign communications.
The article raises a number of issues:
- NSA is indiscriminate in collecting data
- It supports my earlier contention in the original article that it’s access to the data that is key rather than access to actual servers
- Concerning the ridiculous denials by the corporations: Language is key to these denials. Technical language from the domain of networking is used to obfuscate the debate: There is no need for access to ‘servers’ or a ‘back door’ if you have access to a ‘router’, a ‘feed’, a ‘split’ or a ‘tap’.